HarfBuzz is the open-source text shaping engine originally born out of the FreeType project and now widely-used by GNOME, KDE, Java, Flutter, Godot, Chromium, LibreOffice, and countless other applications. HarfBuzz 14.0 released today and making this release quite exciting is introducing a GPU-accelerated text rendering library…
Fedora Rejects Proposal To Use systemd For Managing Per-User Environment Variables
The Fedora Engineering and Steering Committee “FESCo” this week rejected a change proposal for Fedora 45 that would use systemd’s environment generator functionality for managing per-user environment variables…
NVIDIA Provides Preview Driver With DRM Color Pipeline API Support
Following the DRM Color Pipeline API making it into the Linux 6.19 kernel, NVIDIA today released a preview Linux driver with their support for the DRM per-plane color pipeline API that will benefit the broader Linux/Wayland desktop HDR ambitions…
Turbulence at the Documentation Foundation
Michael Meeks has posted an
angry missive about changes at the Document Foundation. What has
really happened is not entirely clear, but it seems to involve, at a
minimum, the forced removal of all Collabora staff from the foundation.
There has been a set of “thank you” notes to the people involved posted in the
foundation’s forums. The Document Foundation’s decision to restart LibreOffice Online almost
certainly plays into this as well.
Details are fuzzy at best; we will be working at providing a clearer
picture, but that will take some time.
The 11 Best Gaming Mice To Dominate Your Competition

Most days around here at HotHardware are frantic, but everyone needs a good work-life balance. As a team populated by mostly PC gamers, we have varying opinions on the best gaming mice currently available. Below are 11 of the top gaming mice to help you dominate the competition, which includes a few highly-rated budget picks, a range of more
The 11 Best Gaming Mice To Dominate Your Competition

Most days around here at HotHardware are frantic, but everyone needs a good work-life balance. As a team populated by mostly PC gamers, we have varying opinions on the best gaming mice currently available. Below are 11 of the top gaming mice to help you dominate the competition, which includes a few highly-rated budget picks, a range of more
AI Pet Translator Uses Machine Learning To Interpret Dog Barks And Cat Meows

If you’ve ever desperately wanted to know exactly what your golden retriever is yelling at the mailman, a newly emerged tech startup claims to have the answer. Enter Pettichat, an AI-powered smart collar currently courting early adopters in its pre-launch phase. Billed as the world’s first real-time, two-way pet translator, the device promises
AI Pet Translator Uses Machine Learning To Interpret Dog Barks And Cat Meows

If you’ve ever desperately wanted to know exactly what your golden retriever is yelling at the mailman, a newly emerged tech startup claims to have the answer. Enter Pettichat, an AI-powered smart collar currently courting early adopters in its pre-launch phase. Billed as the world’s first real-time, two-way pet translator, the device promises
How To Change Your Dorky Gmail Username That You Created 20 Years Ago
Google has finally rolled out a feature that gives users the ability to easily change usernames. This feature initially became available to a subset of users last year, but it’s now available to most users with a Google account.
Making this change is a simple process that involves navigating to the right section within your Google account
How To Change Your Dorky Gmail Username That You Created 20 Years Ago
Google has finally rolled out a feature that gives users the ability to easily change usernames. This feature initially became available to a subset of users last year, but it’s now available to most users with a Google account.
Making this change is a simple process that involves navigating to the right section within your Google account
Sony PS6 Handheld Leak Claims It Beats Xbox Series S In Raster And Ray Tracing

Prominent hardware leaker KeplerL2 made some interesting statements on the NeoGAF forums recently, claiming that the PlayStation 6 Portable is not only faster than the Xbox Series S in raster performance, but “massively ahead” in ray tracing and path tracing performance too. Additionally, the leak asserts that AMD FSR 5 and PSSR 3 will have
Sony PS6 Handheld Leak Claims It Beats Xbox Series S In Raster And Ray Tracing

Prominent hardware leaker KeplerL2 made some interesting statements on the NeoGAF forums recently, claiming that the PlayStation 6 Portable is not only faster than the Xbox Series S in raster performance, but “massively ahead” in ray tracing and path tracing performance too. Additionally, the leak asserts that AMD FSR 5 and PSSR 3 will have
Top 5 Zwift Videos: Zwift in Mallorca, This Season on Zwift, and Tough Races
Zwifters recently descended on Mallorca for Zwift Community Live 2026, an IRL event bringing people together from around the world for 3 days of epic riding. In this week’s top video, watch as one Zwifting YouTuber takes on his first group rides ever!
Zwift just shared a roadmap of what’s coming in the next few months with their “This Season on Zwift” press release, so two of our videos feature this info. We’ve also included videos about riding outdoors after a long indoor season, and racing the final stage of the Zwift Games.
Newbie Invited to Cycling’s Biggest Event… I Was Not Ready
Zwift Finally Has a Gravel Map – Plus Everything Else Coming This Season
I Finally Rode Outside After a Winter on Zwift
How tough can an 11km race on Zwift really be?! (I wasn’t ready!)
Huge Changes Are Coming to Zwift!
Got a Great Zwift Video?
Share the link below and we may feature it in an upcoming post!
Intel Wildcat Lake Specs Leak Reveals Up To A 4.8GHz Boost And Dual Xe3 GPU Cores
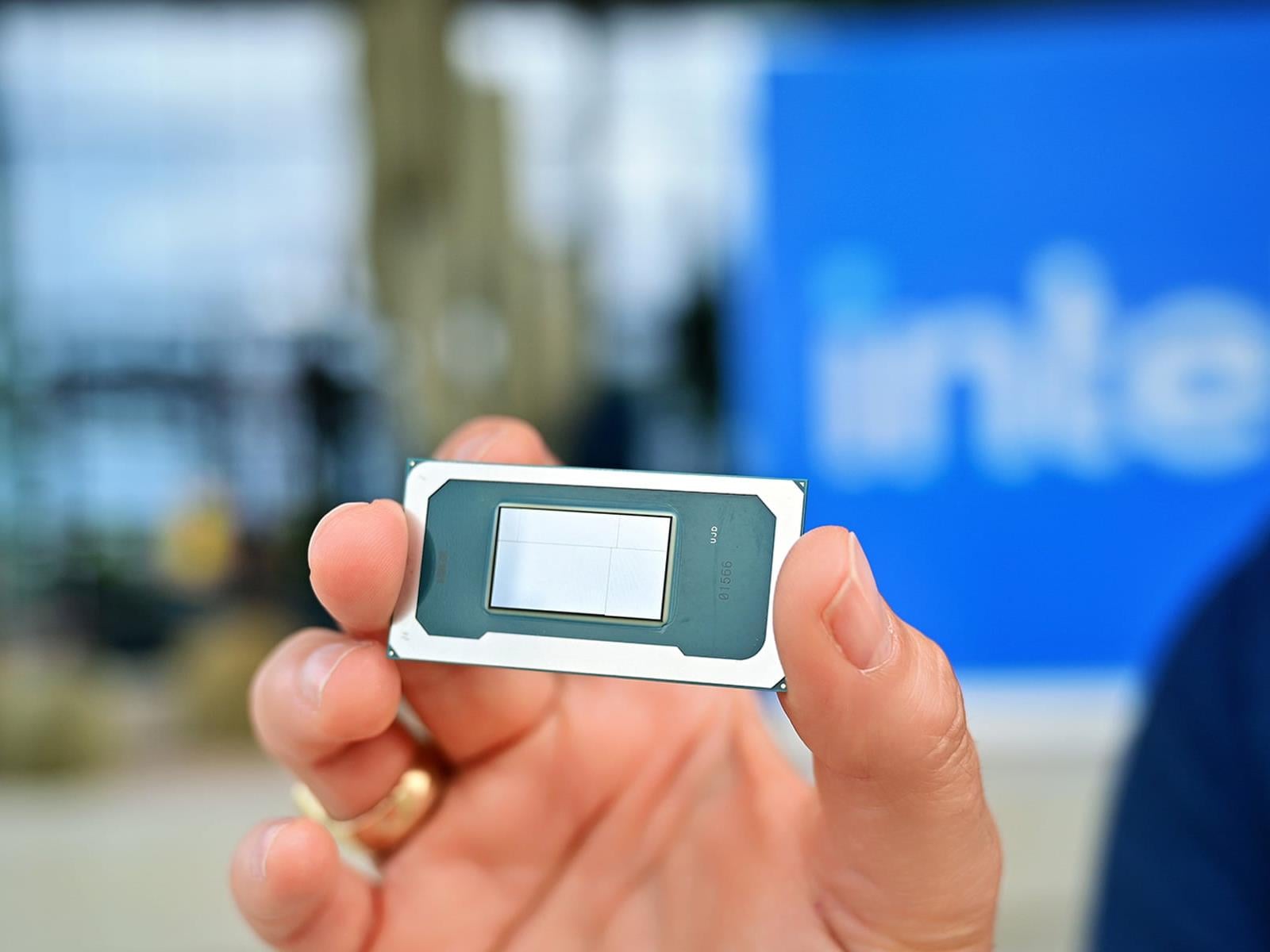
It would be easy to assume from the name that Wildcat Lake is the successor to Intel’s recently launched Panther Lake CPUs, but wildcats aren’t as big as panthers, and there’s your clue as to what these CPUs actually are: the successors to Twin Lake, which was the refreshed version of Alder Lake-N. We already know a fair bit about Wildcat
Intel Wildcat Lake Specs Leak Reveals Up To A 4.8GHz Boost And Dual Xe3 GPU Cores
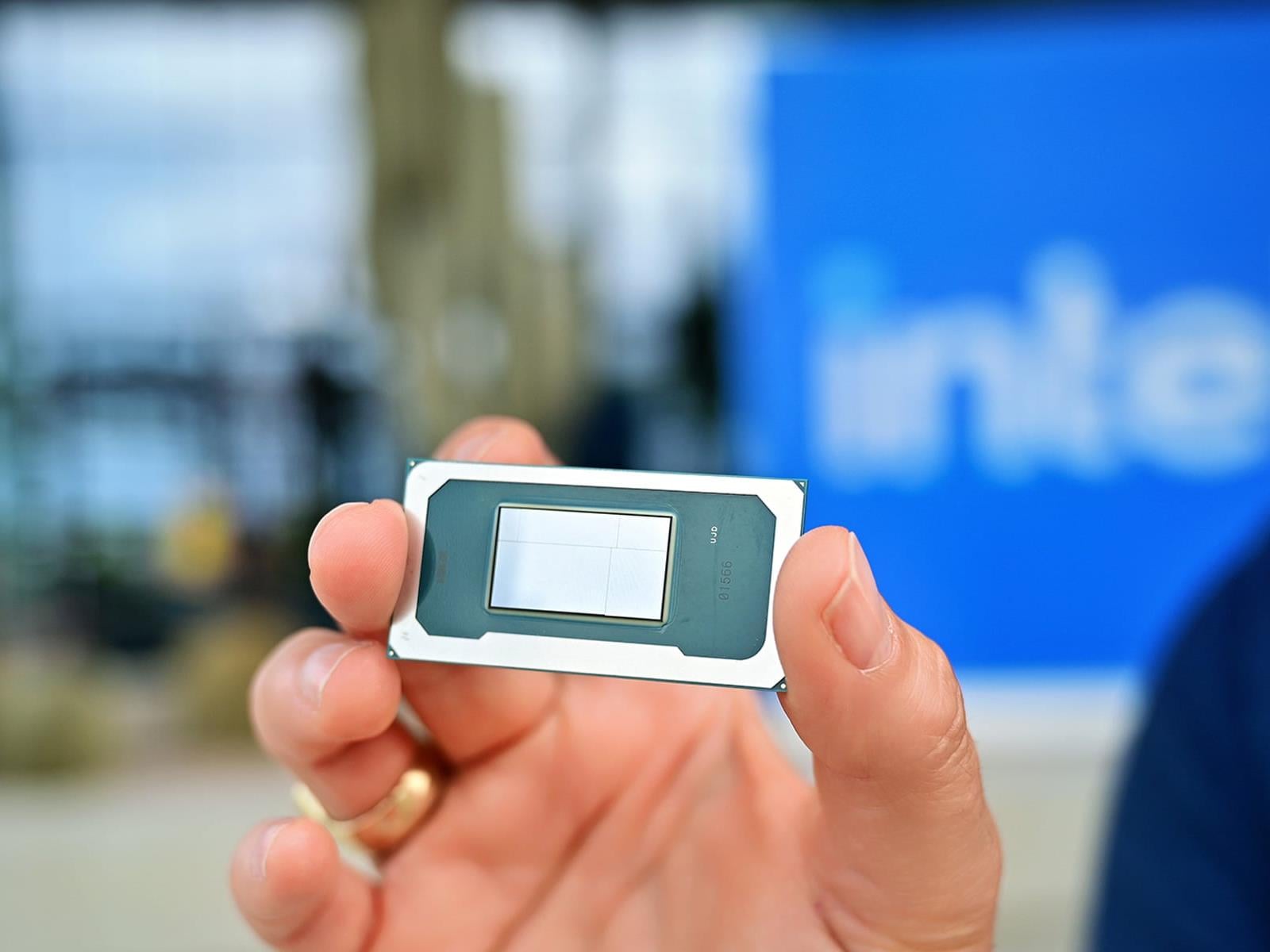
It would be easy to assume from the name that Wildcat Lake is the successor to Intel’s recently launched Panther Lake CPUs, but wildcats aren’t as big as panthers, and there’s your clue as to what these CPUs actually are: the successors to Twin Lake, which was the refreshed version of Alder Lake-N. We already know a fair bit about Wildcat
Nothing Eyes AI Smart Glasses Launch In 2027 To Challenge Apple And Meta

The tech world is currently fixated on the face it seems. As Meta and Apple race to claim the smart glasses crown, London-based Nothing, typically known for phones with transparent aesthetics and glyph-lighting, is evidently preparing its own entry for the first half of 2027.
However, the move into AR and smart eyewear comes at a volatile
Nothing Eyes AI Smart Glasses Launch In 2027 To Challenge Apple And Meta
The tech world is currently fixated on the face it seems. As Meta and Apple race to claim the smart glasses crown, London-based Nothing, typically known for phones with transparent aesthetics and glyph-lighting, is evidently preparing its own entry for the first half of 2027.
However, the move into AR and smart eyewear comes at a volatile
Starlink Satellite Breaks Apart In Orbit As SpaceX Confirms Major Hardware Anomaly

SpaceX has confirmed an orbital anomaly involving a Starlink satellite that fragmented into dozens of pieces, raising fresh concerns about space debris even as the company maintains that the event poses no threat to major upcoming missions like Artemis II. The incident marks the second fragment creation event for the constellation in recent
Starlink Satellite Breaks Apart In Orbit As SpaceX Confirms Major Hardware Anomaly

SpaceX has confirmed an orbital anomaly involving a Starlink satellite that fragmented into dozens of pieces, raising fresh concerns about space debris even as the company maintains that the event poses no threat to major upcoming missions like Artemis II. The incident marks the second fragment creation event for the constellation in recent
Razer Unveils Pro Type Ergo Wireless Keyboard With AI And Space Bar Tricks

Razer is adding to its extensive lineup of keyboards with a new model aimed at combining ergonomics, productivity, and performance in a split design, and this time it’s not a limited edition drop. Called the Pro Type Ergo, Razer’s first ever split keyboard is available now for $189.99, and it comes with some notable features like a center
