At a time when consumers are finding it difficult to get their hands on a new Raspberry Pi, MangoPi is teasing a new single-board computer that is slightly smaller than an SD card.
Source: LXer – Mysterious new Raspberry Pi alternative is the size of an SD card
Monthly Archives: March 2022
First Complete Gap-Free Human Genome Sequence Published
An anonymous reader quotes a report from the Guardian: More than two decades after the draft human genome was celebrated as a scientific milestone, scientists have finally finished the job. The first complete, gap-free sequence of a human genome has been published in an advance expected to pave the way for new insights into health and what makes our species unique. Until now, about 8% of the human genome was missing, including large stretches of highly repetitive sequences, sometimes described as “junk DNA.” In reality though, these repeated sections were omitted due to technical difficulties in sequencing them, rather than pure lack of interest.
Sequencing a genome is something like slicing up a book into snippets of text then trying to reconstruct the book by piecing them together again. Stretches of text that contain a lot of common or repeated words and phrases would be harder to put in their correct place than more unique pieces of text. New “long-read” sequencing techniques that decode big chunks of DNA at once — enough to capture many repeats — helped overcome this hurdle. Scientists were able to simplify the puzzle further by using an unusual cell type that only contains DNA inherited from the father (most cells in the body contain two genomes — one from each parent). Together these two advances allowed them to decode the more than 3 billion letters that comprise the human genome. The science behind the sequencing effort and some initial analysis of the new genome regions are outlined in six papers published in the journal Science.
Read more of this story at Slashdot.
Source: Slashdot – First Complete Gap-Free Human Genome Sequence Published
How To Create And Manage Disk Partitions With Fdisk In Linux
This tutorial explains what is Fdisk, and how to create and manage disk partitions with Fdisk utility in Linux operating systems.
Source: LXer – How To Create And Manage Disk Partitions With Fdisk In Linux
Itochu Invests in Wingcopter
Akihabara News (Tokyo) — Japanese major trading firm Itochu Corporation has made an investment in the German drone delivery pioneer Wingcopter.
Although the specifics of the “capital and business alliance” between the two firms were not released, the main thrust appears to be the establishment of drone delivery services in Japan utilizing the Wingcopter 198 triple-drop delivery drone, for which Itochu will become the dedicated domestic distributor.
“We expect Japan to become one of the most important regions for drone delivery applications in the upcoming years. Therefore, we are convinced that Itochu, with the network and expertise in a huge variety of business sectors as well as the financial power of a Fortune Global 500 company, will help us serve more Japanese customers and allow us to jointly scale Wingcopter’s operations across Japan,” commented Tom Plümmer, co-founder and CEO of Wingcopter.
The tie-up between the two firms first emerged last December with the signing of an initial sales partner agreement.
However, this is not the first time that Wingcopter has flagged its interest in the Japanese market. Last March, the German drone maker collaborated with All Nippon Airways (ANA) to test strategies for connecting small island communities through drone deliveries of medical supplies. Also, last December it was announced that Japan’s Drone Fund III had made an investment in Wingcopter, helping to focus attention on other opportunities in Japan.

Recent Drone Related Articles
ACSL Launches LTE-Compatible Domestic Drone
JAL-KDDI Drone Venture Lifts Off
Aeronext’s CEO Reappointed to Government Committee
Ibaraki Pachinko Firm Innovates on Drone Delivery
Drone for Detecting Illegal Trash Dumping
A.L.I. Drone Delivery Tests in Rural Kochi
Drone Delivery to High-Rise Vertiport
The post Itochu Invests in Wingcopter appeared first on Akihabara News.
Source: Akihabara News – Itochu Invests in Wingcopter
How to Install Ntopng on Debian 11
Ntopng is a web-based application for tracking the network traffic on your server. Learn how to install ntopng on Debian 11 here.
The post How to Install Ntopng on Debian 11 appeared first on Linux Today.
Source: Linux Today – How to Install Ntopng on Debian 11
Chrome's 'Topics' Advertising System Is Here, Whether You Want It Or Not
slack_justyb writes: After the failure of the Chrome user-tracking system that was called FLoC, Google’s latest try at topic tracking to replace the 3rd party cookie (that Chrome is the only browser to still support) is FLEDGE and the most recent drop of Canary has this on full display for users and privacy advocates to dive deeper into. This recent release shows Google’s hand that it views user tracking as a mandatory part of internet usage, especially given this system’s eye-rolling name of “Privacy Sandbox” and the tightness in the coupling of this new API to the browser directly.
The new API will allow the browser itself to build what it believes to be things that you are interested in, based on broad topics that Google creates. New topics and methods for how you are placed into those topics will be added to the browser’s database and indexing software via updates from Google. The main point to take away here though is that the topic database is built using your CPU’s time. At this time, opting out of the browser building this interest database is possible thus saving you a few cycles from being used for that purpose. In the future there may not be a way to stop the browser from using cycles to build the database; the only means may be to just constantly remove all interest from your personal database. At this time there doesn’t seem to be any way to completely turn off the underlying API. A website that expects this API will always succeed in “some sort of response” so long as you are using Chrome. The response may be that you are interested in nothing, but a response none-the-less. Of course, sending a response of “interested in nothing” would more than likely require someone constantly, and timely, clearing out the interest database, especially if at some later time the option to turn off the building of the database is removed.
With 82% of Google’s empire based on ad revenue, this latest development in Chrome shows that Google is not keen on any moves to threaten their main money maker. Google continues to argue that it is mandatory that it builds a user tracking and advertising system into Chrome, and the company says it won’t block third-party cookies until it accomplishes that — no matter what the final solution may ultimately be. The upshot, if it can be called that, of the FLEDGE API over FLoC, is that abuse of FLEDGE looks to yield less valuable results. And attempting to use the API alone to pick out an individual user via fingerprinting or other methods employed elsewhere seems to be rather difficult to do. But only time will tell if that remains true or just Google idealizing this new API. As for the current timeline, here’s what the company had to say in the latest Chromium Blog post: “Starting today, developers can begin testing globally the Topics, FLEDGE, and Attribution Reporting APIs in the Canary version of Chrome. We’ll progress to a limited number of Chrome Beta users as soon as possible. Once things are working smoothly in Beta, we’ll make API testing available in the stable version of Chrome to expand testing to more Chrome users.”
Read more of this story at Slashdot.
Source: Slashdot – Chrome’s ‘Topics’ Advertising System Is Here, Whether You Want It Or Not
How I customize my Linux window decorations
One thing I especially like about Linux is the amazing and vast array of choices in almost everything. Don’t like one application for something? There are usually several more you can choose from. Don’t like how the desktop works? Pick one of many other desktops. Don’t like the window decorations on your desktop? There are many others you can download and try.
Source: LXer – How I customize my Linux window decorations
Nike Wants To 'Destroy' Unauthorized NFTs — How Will That Work?
An anonymous reader quotes a report from Decrypt: When a company like Nike finds someone using its brand without permission, it can ask the courts to order the unauthorized goods to be destroyed. Nike has done this in the past, but its latest trademark lawsuit comes with a twist — the products it wants to “destroy” are NFTs, which are inscribed permanently on the Ethereum blockchain. The case in question involves Detroit-based StockX, a site that lets people buy and sell used brands, including Nike sneakers. […] In a complaint filed last month in New York federal court, Nike accused StockX of ripping off its brand in order to cash in on a “gold rush market” for NFTs. As a remedy for StockX’s alleged infringement of its trademarks, Nike wants the company to turn over its profits and stop the NFT sneaker sales. It also wants a judge to “order that StockX be required to deliver to Nike for destruction any and all Vault NFTs.”
According to Alexandra Roberts, a trademark law professor at the University of New Hampshire, it’s fairly common for companies to ask to destroy goods that infringe their IP — there’s even a law that entitles them to do that. But whether a court will grant the order is likely to be informed by what the brand owner is looking to destroy. Where do NFTs fit into this? It’s an open question since the courts have never had to address it before. And even if the New York court agrees to order the destruction of the StockX NFTs, there’s the question of how exactly Nike would go about doing that.
Records on the blockchain show that StockX has indeed inscribed the NFTs on Ethereum, which means they are indestructible except in the extremely unlikely event that developers agree to fork the blockchain to get rid of them. According to some, the most practical thing for Nike to do would be to send the NFTs to a so-called burner wallet. This wouldn’t destroy them but still achieve the same purpose: “This means that the best outcome for a brand that is seeking to have NFTs destroyed may be to have them sent to a burn address, which still does not actually destroy them but renders them incapable of being transferred anymore,” writes the Fashion Law Blog.
Read more of this story at Slashdot.
Source: Slashdot – Nike Wants To ‘Destroy’ Unauthorized NFTs — How Will That Work?
Forgotten Pokémon Musical From 2000 Gets 68-Minute Documentary
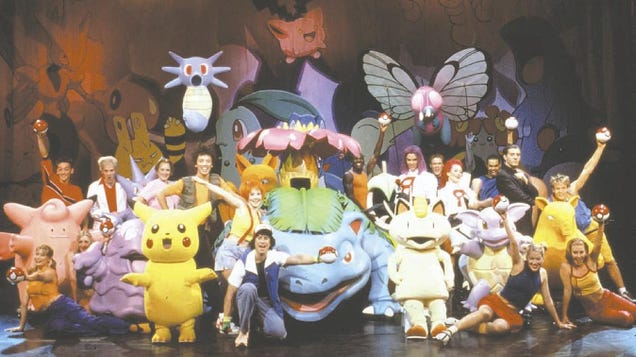
For one brief, shining moment in time over 20 years ago, Pokémon ascended from the anime/video games plane where it normally resides and became something more. Something fancier, something jauntier. And then, just as quickly as it rose, it slipped right back down again, and most folks now forget it ever happened at…
Source: Kotaku – Forgotten Pokémon Musical From 2000 Gets 68-Minute Documentary
Apple rushes out patches for two zero-days threatening iOS and macOS users
Enlarge (credit: Getty Images)
Apple on Thursday released fixes for two critical zero-day vulnerabilities in iPhones, iPads, and Macs that give hackers dangerous access to the internals of the OSes the devices run on.
Apple credited an anonymous researcher with discovering both vulnerabilities. The first vulnerability, CVE-2022-22675, resides in macOS for Monterey and in iOS or iPadOS for most iPhone and iPad models. The flaw, which stems from an out-of-bounds write issue, gives hackers the ability to execute malicious code that runs with privileges of the kernel, the most security-sensitive region of the OS. CVE-2022-22674, meanwhile, also results from an out-of-bounds read issue that can lead to the disclosure of kernel memory.
Apple disclosed bare-bones details for the flaws here and here. “Apple is aware of a report that this issue may have been actively exploited,” the company wrote of both vulnerabilities.
Read 3 remaining paragraphs | Comments
Source: Ars Technica – Apple rushes out patches for two zero-days threatening iOS and macOS users
LibreOffice 7.3.2 Office Suite Is Now Available for Download with 74 Bug Fixes
The Document Foundation announced today LibreOffice 7.3.2 as the second point release to the latest and greatest LibreOffice 7.3 open-source, free, and cross-platform office suite series.
Source: LXer – LibreOffice 7.3.2 Office Suite Is Now Available for Download with 74 Bug Fixes
Samsung To Provide Smartphone Parts, Tools, and Repair Guides Starting This Summer
Starting this summer, Samsung says it will sell genuine parts and tools to customers needed to repair its Galaxy S20 and Galaxy S21 smartphones, along with its Galaxy Tab S7+ tablet. Fast Company reports: The company, which is partnering with device repair resource iFixit on the initiative, will also provide access to step-by-step repair guides, and it plans to support more devices and repairs over time. The program is similar to one that Apple announced last fall, allowing users to repair the display, battery, and camera on their iPhones. Samsung says it’s launching the program to “promote a circular economy and minimize e-waste,” though it’s just as likely responding to regulatory pressure. Last year, the Federal Trade Commission (FTC) said it would crack down on illegal repair restrictions, and iFixit expects dozens of states to introduce right-to-repair laws this year. […]
But while phone makers may now feel compelled to supply repair parts and guides to consumers, that doesn’t mean the repairs themselves will be any easier. According to iFixit’s Galaxy S21 teardown, some repairs involve work that’s “unnecessarily sticky and complicated,” requiring a heat gun to pry open the display panel and an isopropyl alcohol bath to loosen the “tar pit” around the battery. At least customers brave enough to make those repairs won’t have any trouble getting the parts and tools they need.
Read more of this story at Slashdot.
Source: Slashdot – Samsung To Provide Smartphone Parts, Tools, and Repair Guides Starting This Summer
Activision Blizzard Removes Company Vaccine Mandate, 'Effective Immediately'

Activision Blizzard Chief Administrative Officer Brian Bulatao (above) emailed all employees of the company earlier today, informing them that “effective immediately” the publisher was removing the mandate for employees working from offices to be fully vaccinated against Covid-19, and hopes to have everyone working…
Source: Kotaku – Activision Blizzard Removes Company Vaccine Mandate, ‘Effective Immediately’
Russians Leaving Chernobyl After Radiation Exposure
According to the Associated Press, Russian troops have left the Chernobyl nuclear power plant after soldiers received “significant doses” of radiation from digging trenches around the closed plant. On February 24, Russians seized control of Chernobyl shortly after declaring their invasion of Ukraine. From the report: Russian forces seized the Chernobyl site in the opening stages of the Feb. 24 invasion, raising fears that they would cause damage or disruption that could spread radiation. The workforce at the site oversees the safe storage of spent fuel rods and the concrete-entombed ruins of the reactor that exploded in 1986. Edwin Lyman, a nuclear expert with the U.S.-based Union of Concerned Scientists, said it “seems unlikely” a large number of troops would develop severe radiation illness, but it was impossible to know for sure without more details. He said contaminated material was probably buried or covered with new topsoil during the cleanup of Chernobyl, and some soldiers may have been exposed to a “hot spot” of radiation while digging. Others may have assumed they were at risk too, he said.
Read more of this story at Slashdot.
Source: Slashdot – Russians Leaving Chernobyl After Radiation Exposure
How to Install Cachet Status Page System on Ubuntu 20.04
Cachet is an open-source status page system. Learn how to install the Cachet status page system on Ubuntu 20.04 here.
The post How to Install Cachet Status Page System on Ubuntu 20.04 appeared first on Linux Today.
Source: Linux Today – How to Install Cachet Status Page System on Ubuntu 20.04
Wyze Cam Security Flaw Gave Hackers Access To Video; Went Unfixed For Almost Three Years
An anonymous reader quotes a report from 9to5Mac: A major Wyze Cam security flaw easily allowed hackers to access stored video, and it went unfixed for almost three years after the company was alerted to it, says a new report today. Additionally, it appears that Wyze Cam v1 — which went on sale back in 2017 — will never be patched, so it will remain vulnerable for as long as it is used.
Bleeping Computer reports: “A Wyze Cam internet camera vulnerability allows unauthenticated, remote access to videos and images stored on local memory cards and has remained unfixed for almost three years. The bug, which has not been assigned a CVE ID, allowed remote users to access the contents of the SD card in the camera via a webserver listening on port 80 without requiring authentication. Upon inserting an SD card on the Wyze Cam IoT, a symlink to it is automatically created in the www directory, which is served by the webserver but without any access restrictions.”
And as if that weren’t bad enough, it gets worse. Many people re-use existing SD cards they have laying around, some of which still have private data on them, especially photos. The flaw gave access to all data on the card, not just files created by the camera. Finally, the AES encryption key is also stored on the card, potentially giving an attacker live access to the camera feed. Altogether, Bitdefender security researchers advised the company of three vulnerabilities. It took Wyze six months to fix one, 21 months to fix another, and just under two years to patch the SD card flaw. The v1 camera still hasn’t been patched, and as the company announced last year that it has reached end-of-life status, so it appears it never will.
Read more of this story at Slashdot.
Source: Slashdot – Wyze Cam Security Flaw Gave Hackers Access To Video; Went Unfixed For Almost Three Years
Steam Deck, Ryzen Servers, Apple M1 On Linux & Milan-X Excited Linux Users In Q1
Here is a look back at the most-read stories on Phoronix during Q1’22 with our daily content around Linux hardware, open-source news, and lots of benchmarking…
Source: Phoronix – Steam Deck, Ryzen Servers, Apple M1 On Linux & Milan-X Excited Linux Users In Q1
How to Add Ubuntu system to OpenLDAP Server
After you’ve completed the OpenLDAP installation, you will also need to add a client machine to authenticate against your OpenLDAP server. In this tutorial, you will learn how to add an Ubuntu 20.04 Linux system to the OpenLDAP server using libnss-ldap and libpam-ldap.
Source: LXer – How to Add Ubuntu system to OpenLDAP Server
E3 2022 Has Officially Been Canceled
After previously canceling its in-person E3 2022 event, the ESA has now informed its partners that there will be no digital event equivalent this year either – meaning E3 2022 has fully been canceled. IGN reports: The news broke via a tweet from Razer PR lead Will Powers, who said that an email had been sent out announcing the cancellation of a digital E3 event. IGN has independently verified the contents of the email as well. The ESA had initially planned for an in-person E3 event this year after having no event in 2020 due to COVID-19 and a digital one in 2021. “We will devote all our energy and resources to delivering a revitalized physical and digital E3 experience next summer,” said the Entertainment Software Association in an official statement to IGN. “Whether enjoyed from the show floor or your favorite devices, the 2023 showcase will bring the community, media, and industry back together in an all-new format and interactive experience.”
“We look forward to presenting E3 to fans around the world live from Los Angeles in 2023.”
Read more of this story at Slashdot.
Source: Slashdot – E3 2022 Has Officially Been Canceled
Confirmed: Avalanche is likeliest explanation for tragic Dyatlov Pass incident

Enlarge / A view of the tent as the rescuers found it on February 26, 1959. The tent had been cut open from inside, and most of the skiers had fled in socks or barefoot. (credit: Public Domain)
In February 1959, nine young Russian hikers perished during a cross-country skiing trek through the northern Ural Mountains. All were very experienced, so investigators were mystified about why the hikers had cut their way out of their tent in the middle of the night and fled into the wilderness to their deaths. Last year, two scientists published their hypothesis that the group had been surprised by a sudden slab avalanche. Now, those scientists are back to address the concerns of their critics in a recent paper published in the journal Communications Earth & Environment.
The “Dyatlov Pass incident,” as it came to be known, takes its name from the 23-year-old radio engineering student who organized the expedition, Igor Dyatlov. (A mountain pass near the site was named Dyatlov Pass as a memorial.) He and his fellow travelers—seven men and two women—were students at the Ural Polytechnical Institute, since renamed Ural Federal University. One member, Yuri Yudin, turned back on January 27 because his rheumatism had flared up, and the knee and joint pain was too severe to continue. He was the only one of the original 10 who survived.
According to diaries and cameras retrieved from the ill-fated campsite, the hikers began to move through the pass on the morning of February 1. Their goal was to set up camp for the night on the other side. But they lost their bearing because of snowstorms and poor visibility and ended up further west, on the eastern slope of Kholat Syakhl. Rather than backtracking to set up camp in a forested area just under a mile (about 1.5 kilometers) down, the team opted to dig a cut into the slope and pitch their tents there for the night. (Yudin speculated that Dyatlov, the team leader, likely didn’t want to lose the altitude they had gained during the day.)
Read 24 remaining paragraphs | Comments
Source: Ars Technica – Confirmed: Avalanche is likeliest explanation for tragic Dyatlov Pass incident
