Germany’s Sovereign Tech Agency announced a new and expanded Sovereign Tech Fellowship program that is now open to community managers and technical writers, beyond just FOSS maintainers from the prior round…
Category Archives: Linux
Apple Announces “Fusion Architecture” With M5 Pro & M5 Max
Apple announced today the new Fusion Architecture with the M5 Pro and M5 Max SoCs that also feature a next-generation GPU…
[$] Free software needs free tools
One of the contradictions of the modern open-source movement is
that projects which respect user freedoms often rely on proprietary
tools that do not: communities often turn to non-free software for
code hosting, communication, and more. At Configuration Management
Camp (CfgMgmtCamp) 2026, Jan Ainali spoke
about the need for open-source projects to adopt open tools;
he hoped to persuade new and mature projects to switch to open
alternatives, even if just one tool, to reduce their dependencies on
tech giants and support community-driven infrastructure.
Garrett: To update blobs or not to update blobs
Matthew Garrett examines
the factors that go into the decision about whether to install a
firmware update or not.
I trust my CPU vendor. I don’t trust my CPU vendor because I want
to, I trust my CPU vendor because I have no choice. I don’t think
it’s likely that my CPU vendor has designed a CPU that identifies
when I’m generating cryptographic keys and biases the RNG output so
my keys are significantly weaker than they look, but it’s not
literally impossible. I generate keys on it anyway, because what
choice do I have? At some point I will buy a new laptop because
Electron will no longer fit in 32GB of RAM and I will have to make
the same affirmation of trust, because the alternative is that I
just don’t have a computer.
Intel Adapting Linux’s LAM In Preparing For ChkTag
Last year AMD and Intel as part of the x86 Ecosystem Advisory Group announced ChkTag for x86 memory tagging across processors to better fight buffer overflows and use-after-free errors. In preparing for ChkTag with future processors, Intel has begun adapting their Linear Address Masking (LAM) support to more nicely jive with it…
KDE Plasma 6.6.2 Improves Support for High-Resolution Mice on Remote Desktops
The KDE project released KDE Plasma 6.6.2 today as the second maintenance update to the latest KDE Plasma 6.6 desktop environment series to address more bugs, crashes, and other issues.
Intel Preps A Lot Of Xe3 Code For Linux 7.1 Kernel
Intel yesterday sent out their first “drm-xe-next” pull request to DRM-Next of new Xe kernel graphics driver improvements they have readied for their eventual upstreaming into the Linux 7.1 kernel…
AMD Makes rocprof-trace-decoder Open-Source
AMD open-sourced the ROCprof Trace Decoder “rocprof-trace-decoder”, a tool useful for developers targeting the AMD GPU compute stack…
Do you have some rope? Then let’s teach about AI concepts
Teaching about AI concepts in schools is a tricky business as there are complicated ideas to be taught.
To teach complex concepts, in computer science, we often use an instructional approach called ‘unplugged’. We use the unplugged approach to teach computing concepts without a computer. Often unplugged activities include using an everyday analogy or a physical fun activity. For example, to teach about algorithms, students might learn how to make a jam sandwich where the recipe and following instructions accurately are similar to an algorithm and the steps within it used to write a program. The jam sandwich activity has now become a popular and key teaching experience for young students across the world, as it teaches a complex but fundamental idea in a simple and fun way.

At the January 2026 Raspberry Pi Foundation Research Seminar, Salomey Afua Addo, a researcher at the University of Cambridge, presented her work about how to teach about AI. She has specifically looked at this in the context of high school students in Ghana, where AI is now part of the mandatory curriculum. In Ghana, most schools do not have access to computers, therefore an unplugged approach to teach about AI is a good idea. Therefore, Salomey developed a set of unplugged activities to teach about a range of AI concepts.
Here, I focus on one of the activities that she presented — one that I think will become another ‘jam sandwich’ experience for students. So if you might teach about AI at some point, then read on.
Neural networks and rope: An unplugged activity
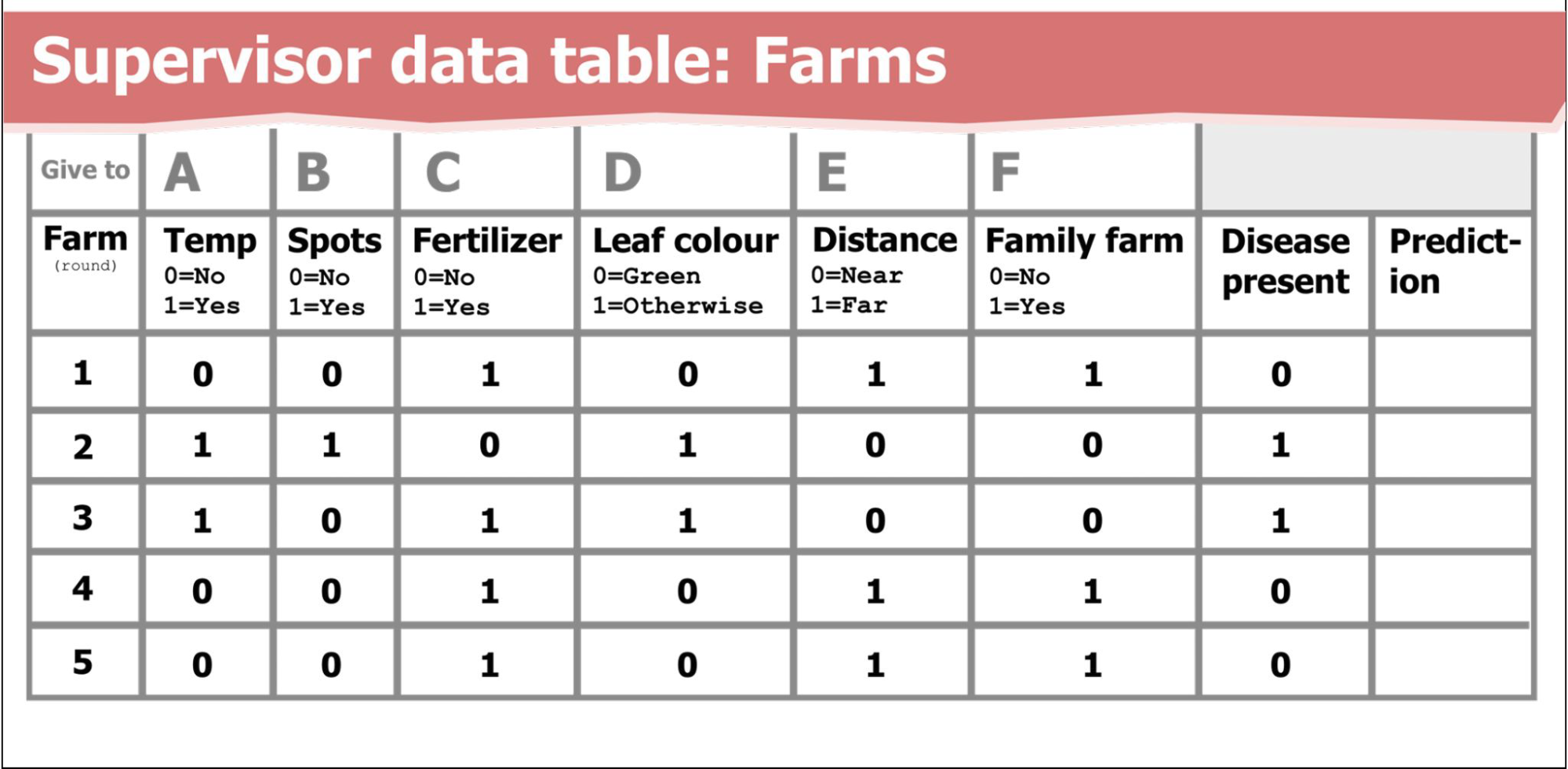
Salomey has designed an unplugged role-play activity to teach about neural networks and how they are trained to solve a problem. She focused on finding a familiar problem context for Ghanaian teachers and their students, and selected farming and crop disease. Students are asked to figure out what features about a farm are relevant for detecting diseases on cocoa trees. To solve the problem, students are given data about the farms (see Table 1). Giving students data, rather than preconceived rules about the context is key to the learning activity. Neural networks are data-driven — they provide a way to model given data so that we can make predictions. Here the features of farms, and importantly whether disease is or is not found in their cocoa trees, is the data that is used to train a model. The model is used to make predictions, which can then be used to improve farming by reducing crop disease.

Using farm data, students can learn how neural networks work, and they can do this through an unplugged role play — using ropes!
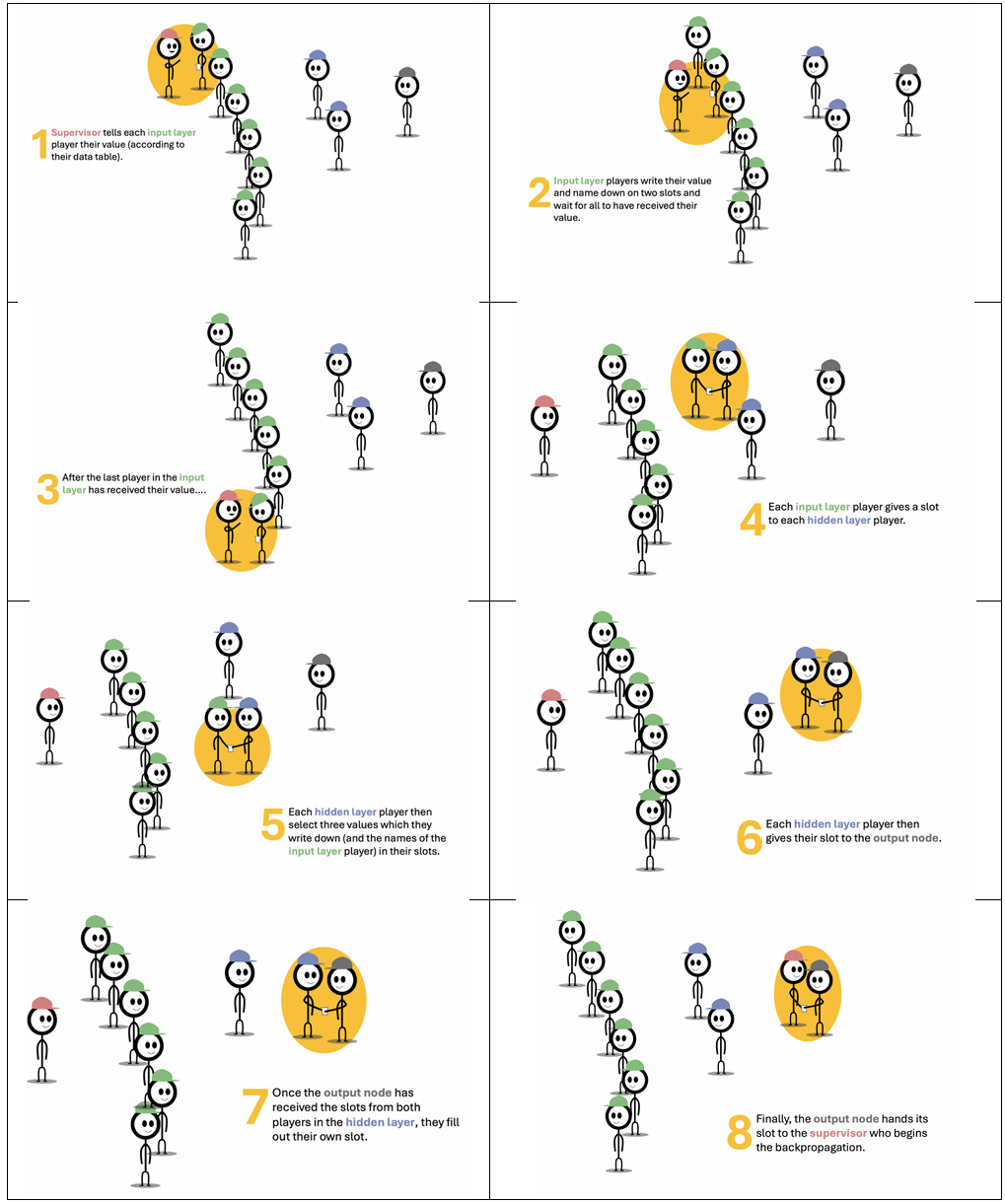
Here’s how Salomey’s classroom activity works. Sets of students act out the processes of training a neural network, including forward propagation, evaluation, and backpropagation. They take on the “roles’’ of some of the concepts of a neural network. One student acts as the supervisor, six students act as the input layer, two as the hidden layer, and one as the output layer.
Keeping it simple: Concepts and data
Key concepts are simplified for students:
- Forward propagation: The hidden layer players randomly select a set of farms (three of the six sets of input values), which reflects how weights are often set to random values at the start.
- Evaluation: The student acting as the output layer compares the prediction (whether crop disease is present or not) to the actual value for the farm to assess the error, similar to a loss function.
- Backpropagation: Inspired by MIT’s RAISE curriculum, this stage is modelled on establishing trust. Players in the hidden and output layers modify their trust in the previous layers (by adding or removing ropes) based on the accuracy of the prediction (if the farm has disease).
Simple numerical data about the features of the problem are given to the students, such as whether the “Temperature” is suitable (0=No, 1=Yes), if there are “Spots” on the plant (0=No, 1=Yes), if “Fertilizer’’ has been used, whether the “Leaf colour’’ is green or not (see Table 1). Importantly, each of the six features given are represented by the six “input layer” students. So each student can ‘process’ each feature as the data for a given farm is used to train the model. Cards are used to represent the data values passed between layers. And this is where the ropes come into play, as they are used to represent the connections between the nodes in the layers.
Instructions for each role
Written role-specific instructions are provided for the students to follow, for example, the Supervisor is given three steps to follow for the forward propagation stage, and the Input Layer students receive a different set of instructions and so on. The detail of the role play is shown in the instruction sheets (see Figure 1).
Why the ropes are important
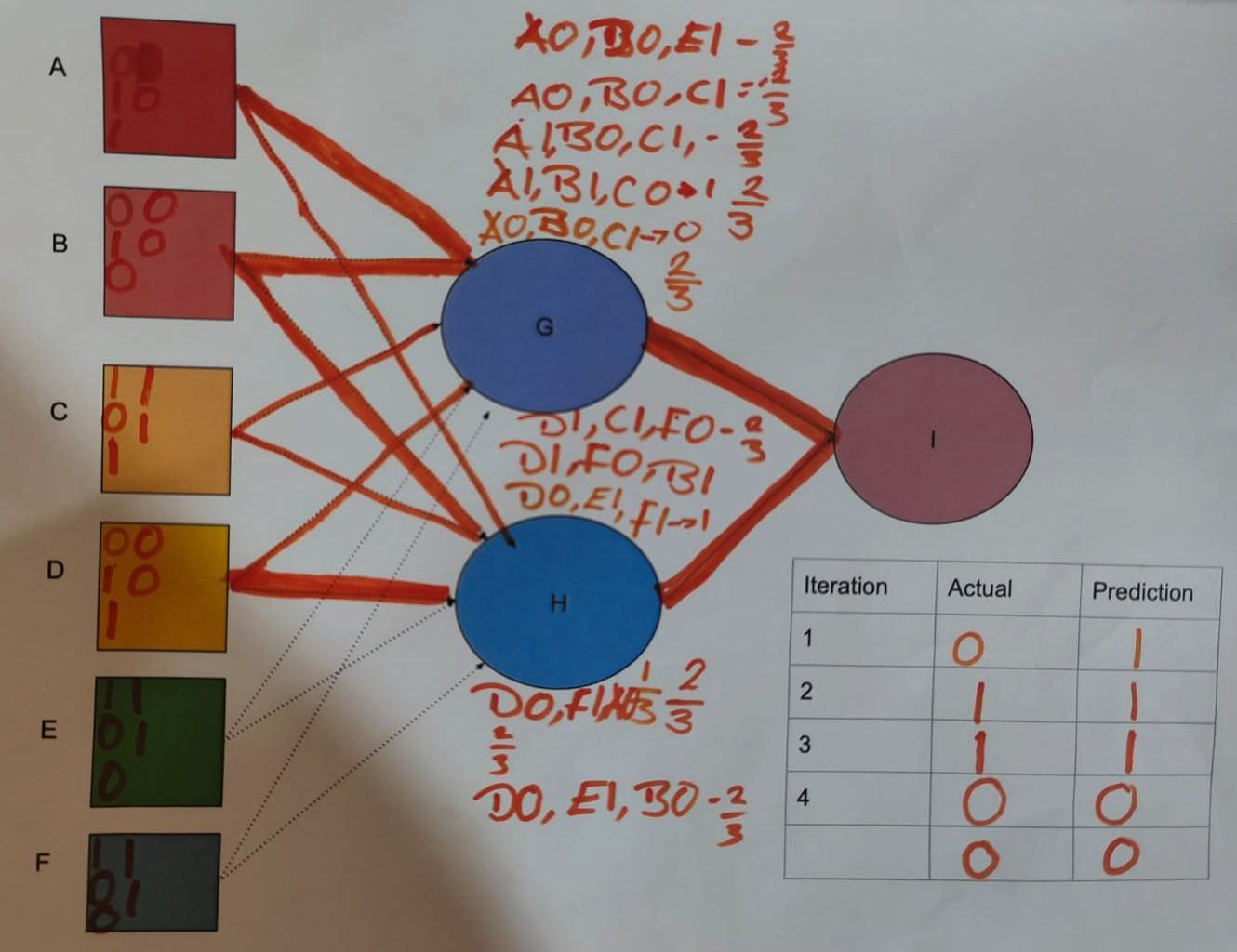
Using ropes to connect the nodes becomes most important at the reverse propagation stage. The clever part of this is that we can show an increase or decrease in the strength of connection by adding or removing ropes. For me, this is the ‘jam sandwich’ effect. This, I think, is probably the most significant learning point. Here, the number of ropes that connect the nodes in the layers are changed based on the strength of evidence that a particular feature is indicated, by the data, to be relevant to the output. In this case, whether “Temperature”, for example, has an implied effect on cocoa disease or not — based on the data, not on any preconceived rule. Simply put, if a farm did have disease then a rope is added, if a farm did not then a rope is removed. Or at a more abstracted level, if a particular neuron contributes towards the correct prediction, a rope is added, otherwise a rope is removed. In a real neural network, backpropagation involves complex maths, such as calculus that would not be accessible to students of this age. Therefore, the rope is an analogy that replaces something that would be impossible for these students to grasp if it was taught using the real-world implementation.
Problem to be solved in the unplugged activity: Identify features that are relevant for detecting diseases
At the end of the activity, features (temperature, leaf color, family farm, etc.) with many rope connections are considered to be relevant for crop disease detection on the farm, whereas features with fewer rope connections are considered to be irrelevant for crop disease detection. The more ropes attached to a particular feature, e.g., temperature, represent its higher relevance in identifying crop disease on the farm.
Activity design, follow-on and evaluation
As part of the design of this activity, Salomey has simplified technical language so that throughout the role play students use everyday terms and she has chosen a context that is relatable for the students. For example, she uses the language of trust, and the new thickness of a rope connection, rather than using technical terms such as weight, loss function, and the error of the network.
Salomey also designed a follow-on activity that uses pen and paper. In this version of the activity, which she calls a board game, the students draw lines to connect the nodes in the layers. The thickness of the lines connecting the nodes represent the strength of the trust (see Figure 2).
Salomey also shared her evaluation of the resources. She conducted pre‑ and post‑intervention surveys with 39 teachers as part of the professional development on the AI teaching materials, and ten of those teachers implemented the unplugged activities in their classrooms. She reported that the teachers found the role-play activity was effective to demonstrate neural networks, that children worked independently to learn, and that some students who did not take part usually in class were engaged.
As well as sharing about her unplugged neural network activity, Salomey also talked about a set of AI stories that she has developed to teach about other aspects of AI applications. For example, the importance of fact-checking is demonstrated through a story about a young girl who fact-checked information she received from her friends about life in a city.
If you would like to find out more about Salomey’s work, you can find related materials on our seminar website.
Join our next seminar
Join us at our next seminar on Tuesday 17 March from 17:00 to 18:30 GMT to hear Rebecca Fiebrink (University of the Arts London) speak about teaching AI for creative practitioners. This will be the second seminar in our new series on how to teach about AI across disciplines. We hope to see you there!
To sign up and take part in our research seminars, click below:
You can also view the schedule of our upcoming seminars, and catch up on past seminars on our previous seminars page.
The post Do you have some rope? Then let’s teach about AI concepts appeared first on Raspberry Pi Foundation.
ARCTIC Cooling Publishes ARCTIC Fan Controller Driver For Linux
A Linux driver has been published for the ARCTIC Fan Controller to be able to read fan speeds under Linux as well as setting the PWM fan speed for each of the ten fans supported by this controller. Making this driver all the more exciting is that ARCTIC Cooling is directly working on this driver rather than just being a community/third-party creation. Furthermore, ARCTIC Cooling is working on getting this driver to the upstream Linux kernel…
FOSS Force’s Top Ten for February, 2026
Here’s what people were reading the most on FOSS Force during the month of February, 2026.
The post FOSS Force’s Top Ten for February, 2026 appeared first on FOSS Force.
Our Fundraising Drive: Like Listener-Supported Radio, Without Breaking Into Programming
Our Independence 2026 Drive has slowed a bit, but readers like Charlie are still going out of their way to keep distro reviews, app coverage, and independent FOSS reporting alive here at FOSS Force.
The post Our Fundraising Drive: Like Listener-Supported Radio, Without Breaking Into Programming appeared first on FOSS Force.
Armbian 26.2 Released with Linux 6.18 LTS, Expanded ARM and RISC-V Support
The Armbian team released Armbian 26.2 today as a major update to this Debian/Ubuntu-based distribution and build framework for ARM devices that enhances performance, security, and hardware compatibility.
DFI IRN556 3.5-inch SBC supports Atom x7000RE and Twin Lake CPUs
DFI has introduced the IRN556, a 3.5-inch single board computer supporting Intel Atom x7000RE “Amston Lake” processors and Intel Processor N-series “Twin Lake” parts. The board targets industrial and embedded deployments requiring extended temperature operation and flexible I/O expansion. The IRN556 supports Intel Atom x7211RE, x7433RE, and x7835RE processors with up to eight cores and […]
GIMP 3.2 RC3 Released In Preparation For The Stable GIMP 3.2
Ahead of the stable GIMP 3.2 release hopefully happening soon, GIMP 3.2 RC3 was released this evening for testing…
IPFire 2.29 Core Update 200 Is Out with Linux 6.18 LTS, IPFire Domain Blocklist
The IPFire project released IPFire 2.29 Core Update 200 today as a new stable update for this open-source hardened Linux firewall distribution that brings various improvements, updated components, and security fixes.
[$] The ongoing quest for atomic buffered writes
There are many applications that need to be able to write multi-block
chunks of data to disk with the assurance that the operation will either
complete successfully or fail altogether — that the write will not be
partially completed (or “torn”), in other words. For years, kernel
developers have worked on providing atomic writes as a way of satisfying
that need; see, for example, sessions from the Linux Storage, Filesystem,
Memory Management, and BPF (LSFMM+BPF) Summit from 2023, 2024,
and 2025 (twice). While atomic direct I/O is now supported by some filesystems, atomic
buffered I/O still is not. Filling
that gap seems certain to be a 2026 LSFMM+BPF topic but, thanks to an early
discussion, the shape of a solution might already be coming into focus.
AMD EPYC Turin 128 Core Comparison: EPYC 9745 “Zen 5C” vs. EPYC 9755 “Zen 5”
The AMD EPYC 9755 128-core Zen 5 server processor has been benchmarked a lot at Phoronix since the EPYC 9005 “Turin” launch as their top-end Zen 5 server processor with “full fat” cores compared to the denser Zen 5C cores that extend up to the EPYC 9965 at 192 cores. For those eyeing the 128 core per socket sweet spot, there is also the EPYC 9745 that is made up of 128 Zen 5C cores that allows for a 400 Watt TDP compared to the 500 Watt EPYC 9755. Today’s benchmarking is comparing the EPYC 9745 and EPYC 9755 performance and power difference.
Firefox 149 beta develops a split personality
A handy feature you can already try in recent versionsThe new beta of the next version of Firefox lets you view two web pages side by side, with a split you can drag with your mouse.…
Høiland-Jørgensen: The inner workings of TCP zero-copy
Toke Høiland-Jørgensen has posted an
overview of how zero-copy networking works in the Linux kernel.
Since the memory is being copied directly from userspace to the
network device, the userspace application has to keep it around
unmodified, until it has finished sending. The sendmsg()
syscall itself is asynchronous, and will return without waiting for
this. Instead, once the memory buffers are no longer needed by the
stack, the kernel will return a notification to userspace that the
buffers can be reused.
